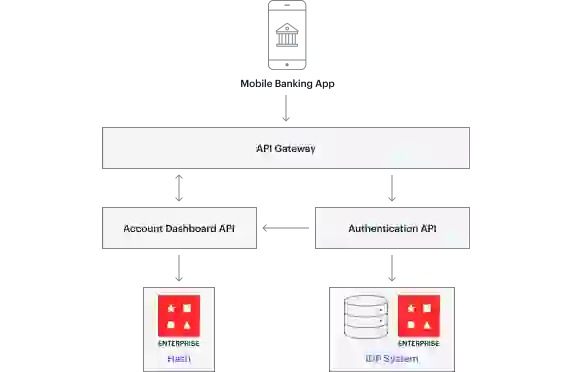
The login and authentication process is critically important to an application’s user experience and availability. During the login process, after the user has successfully enters their credentials, an authentication server creates an authentication token for the duration of the user session. Redis Enterprise excels as an authentication token store. Its speed enables significantly better login experiences while ensuring mission-critical applications are always available and scale seamlessly. Why not make a good first impression?
| The Authentication Challenge | The Redis Enterprise Solution |
|---|---|
| Slow application login and authentication frustrates users and creates a poor first impression. | |
| Difficulty maintaining login and authentication process during periods of peak demand. | |
| Excessive reads cause performance penalties and higher infrastructure costs. |
An authentication token is a digital artifact that represents a user’s identity created by an authentication server after an user has successfully entered their credentials. However, insecure authentication token storage can lead to significant application security vulnerabilities.
The token generated by an authentication server can be stored in a relational or noSQL database, a file-based store, or an in-memory. Disk-based relational or NoSQL databases are slow and pose scalability challenges. In-memory stores such as open-source Redis allow fast access and easy management of tokens but do not scale to meet the needs of today’s companies.
So that applications and their components can quickly and securely identify a user as validated during a user session
Authentication tokens should be stored for the duration of a user session